Apache ActiveMQ Attacks: Hidden Management Interfaces Need Real Oversight
Some of the most dangerous business security problems are not on the desktop. They are the quiet services running behind the scenes.
Apache ActiveMQ Classic is a message broker used to move data between applications, services, and back-office systems. CISA recently added CVE-2026-34197 to its Known Exploited Vulnerabilities catalog after reports of active exploitation. Research from Horizon3.ai explains that the flaw can allow remote code execution through ActiveMQ's Jolokia management API. In some ActiveMQ 6.0.0 to 6.1.1 deployments, a separate issue, CVE-2024-32114, can expose that API without authentication, turning the risk into a no-credential attack path.
For business owners, the lesson is simple: if a management interface is exposed, forgotten, or protected by weak/default credentials, attackers may treat it as a front door.
Why this matters to ordinary businesses
Most companies do not think of message brokers as security priorities. They think about email, Wi-Fi, laptops, servers, accounting software, and cloud apps. But many business systems depend on middleware: tools that pass orders, files, records, alerts, or customer data between applications.
That middleware often runs on Linux or Windows servers, virtual machines, containers, or vendor-managed appliances. It may have been installed years ago for a project and left running because “nothing is broken.” The problem is that attackers actively look for exactly those overlooked systems.
If an exposed ActiveMQ management endpoint is vulnerable, an attacker may be able to run commands on the server. From there, the impact can spread quickly:
- application data may be accessed or changed
- credentials and configuration secrets may be stolen
- malware or web shells may be installed
- other internal systems may be probed
- business workflows may be disrupted
- ransomware staging may begin quietly before anyone notices
This is not just a developer issue. It is an operations and risk-management issue.
What makes management interfaces risky
Management interfaces are powerful by design. They are meant to configure, inspect, restart, and control services. That power is useful for administrators, but dangerous when exposed to the wrong network or protected by weak authentication.
The ActiveMQ/Jolokia situation highlights a common pattern: one vulnerability may be serious on its own, but the real-world risk becomes worse when combined with poor configuration. Default credentials, internet exposure, old versions, missing network restrictions, and weak asset documentation all compound the problem.
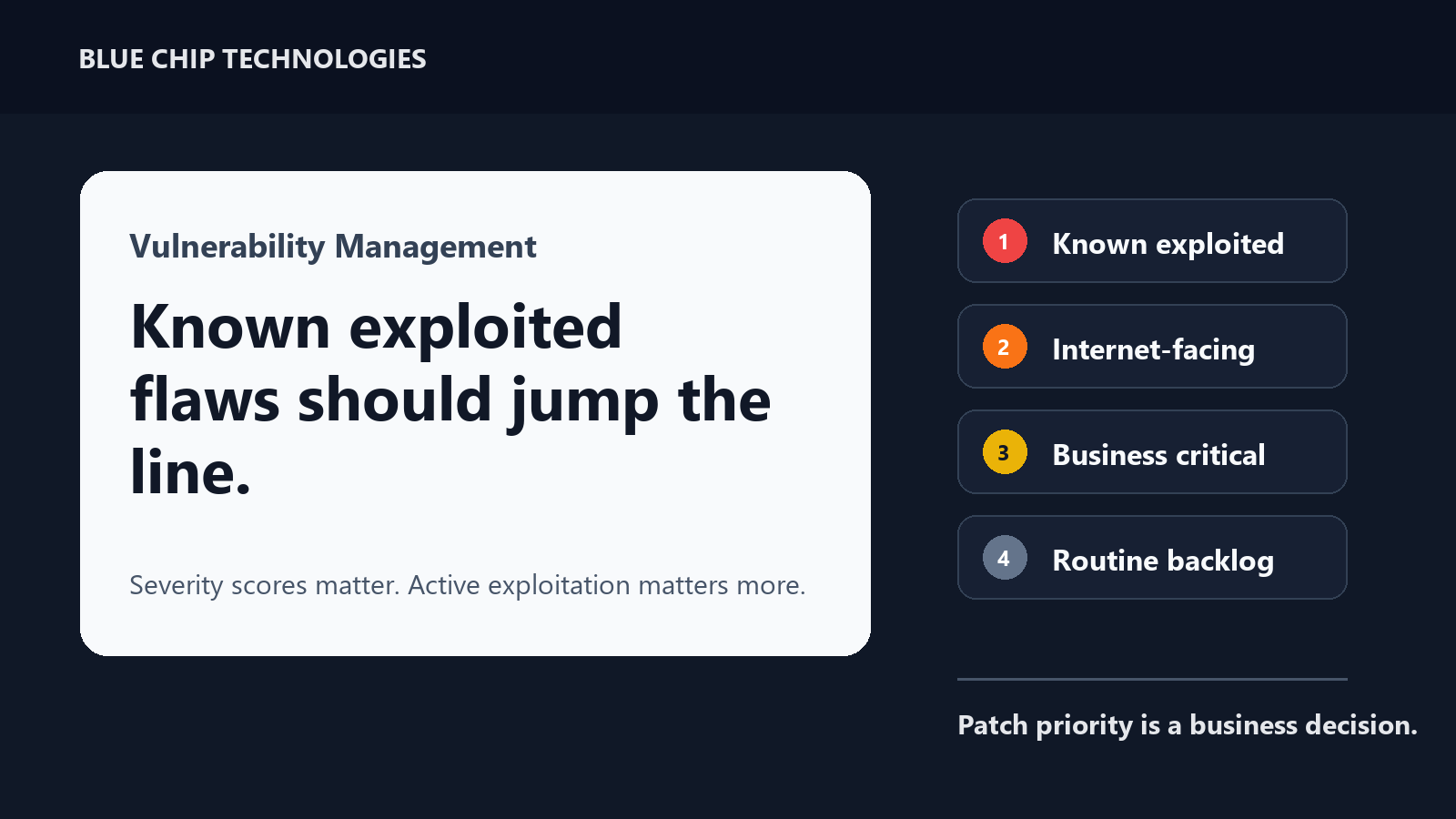
That is why vulnerability management cannot stop at “install updates.” Businesses also need to know what is running, where it is exposed, who can access it, and whether old services still belong in production.
What IT teams should check now
If your business or vendor environment uses Apache ActiveMQ Classic, confirm the version and upgrade to a fixed release recommended by Apache and vendor guidance. Horizon3.ai notes fixes in ActiveMQ Classic 5.19.4 and 6.2.3; administrators should confirm the correct supported version for their deployment.
Then check exposure. Jolokia and web console endpoints should not be open to the public internet. Restrict management access to trusted administrative networks, VPNs, or secure internal paths. Remove default credentials, enforce strong unique passwords, and disable management features that are not required.
Finally, look for signs of compromise. Review broker logs and server activity for unusual Jolokia requests, unexpected outbound HTTP requests from the ActiveMQ process, unknown child processes spawned by Java, new scheduled tasks, suspicious users, unfamiliar files, or changes around the time exploitation activity became public.
Where managed IT helps
Blue Chip's Managed IT Services is built around this kind of operational visibility. We use enterprise remote monitoring and management, automated patch management across Windows, macOS, Linux, and third-party applications, Bitdefender GravityZone endpoint security, EDR, vulnerability management, ransomware prevention, phishing and web threat defence, asset documentation, helpdesk/ticketing, and optional 24/7 NOC support.
For issues like ActiveMQ, the value is not only in knowing that a CVE exists. The value is in having a repeatable process to answer practical questions:
- Do we know which servers and applications exist?
- Are business-critical services documented?
- Are patches being deployed and verified?
- Are management ports exposed where they should not be?
- Are endpoint and server alerts being reviewed?
- Are exceptions tracked instead of remembered informally?
That process turns security from a one-time emergency into normal business maintenance.
The takeaway
The ActiveMQ attacks are a reminder that attackers do not only target laptops and email inboxes. They also target the hidden plumbing that keeps business applications connected.
If you cannot quickly list your servers, middleware, exposed management interfaces, patch status, and security alerts, the vulnerability is only part of the risk. The bigger issue is lack of visibility.
Source: CISA — CISA Adds Apache ActiveMQ CVE-2026-34197 to Known Exploited Vulnerabilities; Horizon3.ai — CVE-2026-34197 ActiveMQ RCE via Jolokia API; The Hacker News — Apache ActiveMQ CVE-2026-34197 Added to CISA KEV Amid Active Exploitation.